In this article, we will explore the concept of cyber security and the security solutions in relation to businesses. We will explore ways to keep data safe and protect against online threats. We'll discuss strategies, technologies, and best practices for ensuring security risks are minimised in today's ever-changing digital world.
By understanding cyber security, businesses can protect their valuable assets from security threats and ensure their confidentiality, integrity, and availability.
In the past year, there has been a decrease in trust in technology due to threats to digital peace. This has emphasised the need for better cyber defences at every level. Centrality and other global companies are investing and collaborating with Microsoft to improve security, which is a positive development for all businesses.
 Why is cybersecurity important?
Why is cybersecurity important?
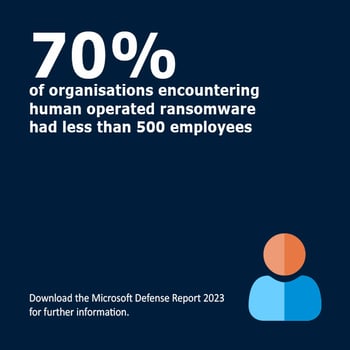
Cybersecurity poses a significant challenge in our era. Organisations worldwide, spanning various industries and sizes, are experiencing pressing needs to improve security measures and safeguard against advanced and relentless attacks.
We firmly believe in empowering companies worldwide to meet their security needs. Achieving this goal requires a collective global effort, as we join forces through partnerships to strengthen our defences together.
The power of collaboration is widely recognized across societies, and it also holds true in the realm of cybersecurity. Embracing multi stakeholder partnerships is key as we strive to address the question of how to ensure a safer and more secure world for all.
While individual organisations focus on safeguarding their own data, network security, security awareness training and endpoint security, their efforts ultimately extend to protecting their customers, constituents, and communities.
Partnerships serve as a powerful catalyst for all those engaged in cybersecurity.
Collaborative initiatives among stakeholders - including government agencies, private sector entities, academia, non-profits, and other organisations - are vital in establishing robust defences against cyber threats. Collective efforts enhance resilience and enable the development of effective countermeasures.
Is real-time attack detection the future of cyber security?
With its ability to instantly identify and respond to cyber threats, this cutting-edge technology holds the potential to revolutionise the way we safeguard our digital assets. By continuously monitoring and analysing network traffic in real-time, it empowers organisations to proactively mitigate risks and fortify their defences against even the most sophisticated cyber attacks.
As the landscape of cyber threats continues to evolve, real-time attack detection emerges as a critical component in the battle against cybercrime. Companies have to stay ahead of the curve and embrace this game-changing solution to protect valuable data and secure digital infrastructure. The future of cyber security starts with real-time attack detection.
What does cybersecurity mean to you?
The concept of cybersecurity can vary among organisations. Many organisations prioritise protection against data breaches and phishing attacks. For organisations with numerous remote workers, often working on mobile devices, it is paramount to understand the potential cybersecurity risks they pose. Therefore, the protection steps taken by each organisation should be tailored specifically to their needs and the type of cyber protection they require.
On the other hand, take credit card data handling organisations, for example. Cybersecurity is crucial for them as it can determine their compliance with the PCI DSS (Payment Card Industry Data Security Standard).
 Will AI replace IT cybersecurity?
Will AI replace IT cybersecurity?
Artificial intelligence (AI) is revolutionising the field of cybersecurity, enabling organisations to proactively mitigate threats by harnessing the power of advanced algorithms and machine learning. However, effectively utilising AI to stay ahead of these constantly evolving threats entails the collection and analysis of vast and diverse datasets from various sources.
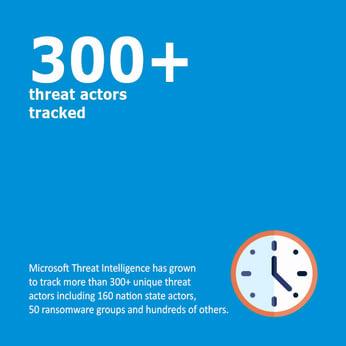
By leveraging both 10,000 security experts and AI, Microsoft diligently analyses over 65 trillion signals, monitoring threats from multiple threat actor groups globally. You can benefit from this intelligence partnering your company with Centrality, a Microsoft Solutions Partner.
How will AI be used to improve cybersecurity in 2024?
In future years, the unprecedented advancements in AI are set to revolutionise the field of cybersecurity. By harnessing the power of artificial intelligence, organisations will be able to deploy sophisticated algorithms and machine learning models to detect and prevent emerging threats in real-time.
AI-based cybersecurity systems will be capable of continuously analysing vast amounts of data, identifying patterns, and flagging suspicious activities to ensure enhanced protection against cyber attacks.
This proactive approach, coupled with the ability to swiftly adapt and respond to evolving threats, will undoubtedly play a vital role in safeguarding digital infrastructure and preserving the integrity of sensitive information in 2024 and beyond.
How can you protect against 99% of attacks?
Here are key steps you can implement to ensure the security of your organisation's environment:
- Enabling multi factor authentication (MFA) is crucial as it adds an extra layer of security to safeguard against compromised user passwords. It also enhances the resilience of identities, providing valuable protection. Let's ensure your accounts are well-protected!
against compromised user passwords and helps to provide extra resilience for identities. - Applying Zero Trust principles: Effective resilience planning is crucial in minimising the impact of attacks on organisations. By establishing a strong foundation, organisations can better protect themselves and mitigate potential risks. Zero trust principles;
-
-
- Explicitly Verify: Before allowing access to resources, it is important to verify the state of users and devices beforehand.
- Use least privilege access: It is advisable to grant only the necessary privileges and no additional ones.
- Assume breach: Assume defences and systems have been compromised, continuously monitoring the environment to detect potential attacks.
-
- Use extended detection and response (XDR) and antimalware: Using software to detect and automatically block attacks, along with obtaining insights for security operations software, allows for timely responses to threats. Monitoring insights from threat detection systems is crucial in ensuring effective threat management.
- Keep up to date: Unpatched and outdated systems are a leading cause for organisations falling prey to attacks. It is crucial to regularly update all systems, firmware, operating systems and applications to stay ahead of potential vulnerabilities and protect against cyber threats.
- Protect data: Having a comprehensive understanding of your critical data, its location, and the implementation of appropriate defences is absolutely crucial when it comes to ensuring the right level of protection.
Switching your organisation to hyperscale cloud, like Microsoft Azure, simplifies the implementation of essential security practices, either by enabling them by default or eliminating the need for you to implement them.
With the advent of software-as-a-service (SaaS) and platform-as-a-service (PaaS) solutions, businesses now have the option to entrust cloud providers with patch management. This not only ensures you're secure, whilst giving you visibility of how up-to-date your system is, but also offers a preferred choice for many. Embracing the convenience and reliability of cloud services for your business means an automatic benefit from improved protection.
In Summary
Centrality is committed to empowering companies worldwide, by encouraging and fostering collaboration, to address their security needs. Microsoft Threat Intelligence actively monitors over 300 threat actors, encompassing nation-state agents and ransomware groups, so as a Microsoft Solutions Partner who holds the Security designation we can use this to benefit you and your organisation.
Real-time attack detection and AI-driven cybersecurity are integral components for future-proof protection against cyber threats. Implementing multi-factor authentication and embracing Zero Trust principles are crucial for effectively safeguarding against attacks. We can help you with this. If you would like to find out more about how to protect your organisation, talk to one of our experts today or visit our cyber security services page.
This article was written with reference to the Microsoft Digital Defence Report 2023, which can be downloaded using the link.



